How to monitor digital asset market risk effectively

Institutional exposure to digital assets has never been higher, and neither has regulatory scrutiny. Finance and risk teams are now expected to operate with the same rigor they apply to traditional asset classes, but in a market that moves faster, lacks standardized data, and regularly produces novel failure modes. A single custody incident or counterparty collapse can trigger regulatory investigations, reputational damage, and material losses simultaneously. The good news is that a structured, evidence-based risk monitoring framework can bring genuine clarity and control to what often feels like an unmanageable problem.
Table of Contents
- Laying the groundwork: Key requirements and tools
- Step-by-step: Building your market risk monitoring framework
- Mitigating risks: Controls, custody, and compliance
- Ongoing verification: Blockchain analytics, reporting, and regulatory updates
- The hard truths behind digital asset risk monitoring success
- Upgrade your digital asset risk strategy with DARE
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive frameworks | A robust risk monitoring process requires multilayered frameworks, clear metrics, and ongoing compliance. |
| Model selection matters | Choosing advanced models like GARCH-family enhances the detection of volatility and market tail risks. |
| Integrated controls | Effective risk mitigation uses custody tools, blockchain analytics, and timely regulatory reporting. |
| Continuous monitoring | Markets change quickly so real-time analytics and alerting are vital to stay ahead of risk. |
Laying the groundwork: Key requirements and tools
Now that you’ve seen the stakes, let’s break down what’s actually required to construct a regulatory-compliant monitoring setup.
Before you configure a single alert or write a single policy, you need to understand the regulatory landscape you’re operating in. The Financial Action Task Force (FATF) sets global standards for anti-money laundering and counter-terrorist financing that apply directly to virtual asset service providers. The Virtual Assets Regulatory Authority (VARA) in Dubai, the Markets in Crypto-Assets (MiCA) regulation in Europe, and various national frameworks all impose specific documentation and governance requirements. Regulatory-compliant risk frameworks require business-wide risk assessments covering products, customers, and geographies, with documented scoring methodologies reviewed annually and aligned to these standards.
The technical toolkit for digital asset risk monitoring is distinct from traditional finance. You need blockchain analytics platforms capable of tracing on-chain transactions, risk scoring engines that can process real-time data, and custody integrations that feed into your monitoring stack. Here’s a breakdown of the core risk categories and the tools that address them:
| Risk category | Description | Primary monitoring tool |
|---|---|---|
| Market risk | Price volatility, liquidity gaps | VaR models, volatility analytics |
| Counterparty risk | Exchange or custodian default | Proof-of-reserves, on-chain monitoring |
| Custody risk | Key management failures, theft | HSM audits, transaction monitoring |
| Compliance risk | AML/CFT violations, sanctions | Blockchain analytics, wallet screening |
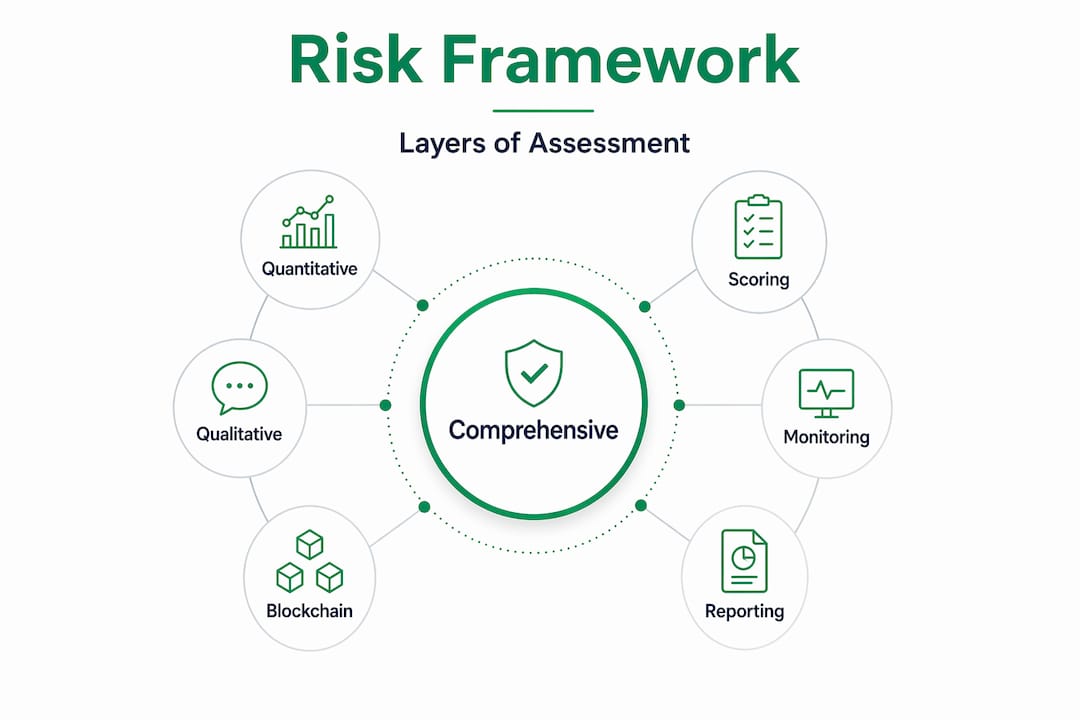
Comprehensive risk assessment frameworks categorize risks using multilayered blockchain risk scoring, incorporating quantitative metrics like volatility, transaction history, network adoption, and on-chain data for compliance and exposure limits. This multilayered approach is what separates institutional-grade monitoring from basic price alerts.
Your governance documentation must be in place before you go live. This means a written risk appetite statement, board-approved policies for digital asset exposure, and a clear escalation matrix. Every tool you deploy needs to feed into a documented process, not just a dashboard.
Pro Tip: Map each risk category to a specific data source and a named owner before you select your technology stack. Governance gaps are almost always ownership gaps in disguise.
Building digital asset risk readiness into your organization’s culture from the start is far more effective than retrofitting compliance after an incident.
Step-by-step: Building your market risk monitoring framework
With requirements in place, it’s time to establish the actual mechanics of real-time market risk monitoring.
A well-constructed framework follows a logical sequence. Skipping steps creates blind spots that only become visible during a crisis, which is exactly the wrong time to discover them.
-
Define your asset universe. List every digital asset your organization holds, trades, or has indirect exposure to through counterparties. Include stablecoins, tokenized assets, and DeFi positions. Each asset type carries distinct risk characteristics.
-
Assign quantitative risk scores. Use multilayered scoring that incorporates price volatility, on-chain transaction volume, network adoption metrics, and liquidity depth. A Bitcoin position and an illiquid altcoin position require fundamentally different risk treatments.
-
Select your volatility model. VaR-based frameworks using GARCH-family models such as TGARCH for Bitcoin and EGARCH for Ethereum, combined with skewed-t distributions and volatility clustering, are the current institutional standard for detecting tail risks in crypto assets. The choice of model matters because crypto volatility is asymmetric and fat-tailed in ways that standard normal distribution models miss entirely.
-
Implement counterparty monitoring. Institutions track counterparty default risk using CEX risk models, proof-of-reserves validation, on-chain monitoring, and exchange concentration indices. For each exchange or custodian you use, you should have a live dashboard showing their on-chain reserve levels and any unusual outflow patterns.
-
Set exposure limits and early-warning triggers. Define hard limits for single-asset concentration, single-counterparty exposure, and total portfolio VaR. Then set warning thresholds at 70% and 85% of each limit so you have time to act before a breach.
-
Document and test. Run stress scenarios quarterly. Simulate a 40% single-day price drop, a custodian halt, and a regulatory freeze simultaneously. Your framework should produce a clear response playbook for each scenario.
Here’s a comparison of the most common volatility models used in institutional crypto risk management:
| Model | Best for | Key strength | Limitation |
|---|---|---|---|
| GARCH | General volatility clustering | Widely validated, easy to explain | Assumes symmetric shocks |
| TGARCH | Bitcoin, asymmetric volatility | Captures leverage effects | More parameter estimation required |
| EGARCH | Ethereum, log-variance modeling | No non-negativity constraints | Complex interpretation |
| Historical simulation | Tail risk, fat-tailed assets | No distributional assumptions | Requires long data history |
Pro Tip: Don’t use a single model in isolation. Run TGARCH and historical simulation in parallel for major positions, and flag divergences between the two as a signal for deeper review.
Connecting institutional risk models for digital assets to your existing enterprise risk management infrastructure is critical. Siloed crypto risk tools that don’t feed into your firm’s central risk reporting create dangerous blind spots at the portfolio level.

Mitigating risks: Controls, custody, and compliance
After your framework is live, persistent risk exposure demands robust controls and ongoing compliance strategies.
Monitoring without mitigation is just observation. Your framework needs a set of active controls that respond automatically or through defined human workflows when thresholds are breached.
Core mitigation measures include:
- Diversification across custodians and exchanges. No single counterparty should hold more than a defined percentage of total digital asset holdings. Post-FTX, most institutional risk policies set this at 20% to 30% maximum per counterparty.
- Collateral management. For lending or derivatives positions, require overcollateralization and define margin call triggers that fire well before default risk materializes.
- Real-time on-chain monitoring. Counterparty risk metrics include Exposure at Default (EAD), Potential Future Exposure (PFE), and Value at Risk (VaR), with mitigation via collateral, netting, diversification, and real-time on-chain monitoring, especially critical in the post-FTX environment where off-chain reporting proved unreliable.
- Netting agreements. Where legally enforceable, bilateral netting reduces gross counterparty exposure significantly.
Custody deserves its own section because it’s where most institutional losses actually occur. Custody risk assessment evaluates key management using hardware security modules (HSMs) and multisig schemes, security infrastructure, real-time transaction monitoring, velocity controls, and address whitelisting. Every one of these elements needs to be documented, tested, and audited on a defined schedule.
“The difference between a recoverable incident and a catastrophic loss in digital asset custody almost always comes down to whether velocity controls and address whitelisting were implemented before the attack, not after.”
Compliance controls require specific attention to edge cases. Privacy coins like Monero or Zcash trigger enhanced due diligence (EDD) requirements under most regulatory frameworks because their transaction graphs are opaque to standard blockchain analytics. Unhosted wallets, meaning wallets not held by a regulated custodian, require additional counterparty verification steps. Transactions involving high-risk jurisdictions on FATF’s gray or black lists require documented risk acceptance at the senior management level.
Board approval and annual review cycles are not optional formalities. Regulators increasingly treat the absence of documented board oversight as evidence of systemic governance failure, which carries its own penalty risk separate from any underlying compliance violation.
Ongoing verification: Blockchain analytics, reporting, and regulatory updates
Risk management is never static. Here’s how to ensure your monitoring process remains effective and compliant.
A framework that was current twelve months ago may already have gaps. Regulatory standards evolve, new asset types emerge, and threat actors adapt their methods. Ongoing verification is what separates a living risk program from a compliance document that sits on a shelf.
-
Deploy blockchain analytics for continuous visibility. Blockchain analytics enable tracing of fund flows across wallets and chains for AML/CFT purposes, assessing both direct and indirect exposure in ways that traditional direct risk assessment cannot. This means you can identify exposure to sanctioned addresses or high-risk mixing services even when the connection is two or three hops removed from your direct counterparty.
-
Automate alert workflows. Configure alerts for unusual outflows from custodian addresses, large position concentration changes, volatility spikes that approach your VaR limits, and wallet interactions with flagged addresses. Alerts should route to named individuals with defined response timeframes, not just into a general inbox.
-
Produce regular risk reports. Monthly reports for internal risk committees, quarterly reports for the board, and annual reports aligned to your regulatory submission cycle. Each report should include a trend analysis, not just a point-in-time snapshot.
-
Schedule regulatory horizon scanning. Assign someone to monitor FATF guidance updates, local regulatory consultations, and enforcement actions in your operating jurisdictions. New guidance often signals where the next examination focus will land.
-
Conduct annual framework reviews. Treat each annual review as a genuine reassessment, not a rubber stamp. Bring in external validators where possible to challenge your assumptions.
Pro Tip: Keep a running log of every alert generated, every investigation triggered, and every decision made. Regulators don’t just want to see your framework. They want to see evidence that it actually runs.
The hard truths behind digital asset risk monitoring success
The operational processes are now clear. Let’s challenge some common industry assumptions and share lessons that don’t usually appear in vendor white papers.
The most dangerous misconception in institutional digital asset risk management is that a well-documented framework equals a well-managed risk. Documentation is necessary but not sufficient. We’ve seen organizations with beautifully formatted risk policies that had never actually run a stress test or reviewed a blockchain analytics alert in practice. When regulators or auditors probe beyond the documentation, the gaps become immediately apparent.
The over-reliance on proof-of-reserves is a specific vulnerability worth naming directly. After FTX, many institutions implemented proof-of-reserves checks and considered the counterparty risk problem solved. It isn’t. Proof-of-reserves limitations are well-documented: a snapshot of reserves at a single point in time tells you nothing about the velocity of outflows, the quality of the assets backing those reserves, or whether liabilities are being accurately reported. On-chain flow monitoring, watching for unusual large outflows from exchange hot wallets in real time, provides the early warning signal that static proof-of-reserves cannot.
The future of effective risk monitoring is multi-source, real-time, and behavioral. It combines on-chain analytics, network-level signals, counterparty financial data, and regulatory intelligence into a single operational picture. That’s a significant capability investment, but it’s also the direction that both regulators and institutional best practice are moving toward.
Perhaps most importantly, sustainable risk management in digital assets requires a genuine risk culture, not just a risk function. Every team member who touches digital assets, from treasury to legal to operations, needs to understand their role in the monitoring process. Checklists and dashboards are tools. The people who use them are the actual control. Readiness evaluation insights consistently show that organizations with strong risk cultures identify and contain incidents faster than those that rely on technology alone.
Upgrade your digital asset risk strategy with DARE
If you’re ready to take your risk monitoring to the next level, here’s how DARE can help.
The framework outlined in this guide represents current institutional best practice, but implementing it correctly requires more than technical knowledge. It requires structured assessment, documented governance, and credentials that regulators and counterparties recognize.
The Digital Asset Readiness Evaluation (DARE) platform provides exactly that. DARE offers modular assessments covering market risk, custody, compliance, and operational controls, mapped to the regulatory standards your team is already working toward. Annual renewal cycles ensure your certification stays current as standards evolve. When you evaluate your digital asset readiness through DARE, you’re not just checking a box. You’re building the documented, validated governance infrastructure that protects your organization and demonstrates credibility to regulators, auditors, and counterparties.
Frequently asked questions
What is the most effective metric for digital asset market risk?
Combining Value at Risk (VaR) with counterparty exposure metrics like EAD and PFE provides a comprehensive view that captures both market price risk and the credit dimension of counterparty default.
How can blockchain analytics enhance risk monitoring?
They trace fund flows across wallets and chains, exposing indirect exposure to sanctioned or high-risk addresses and supporting AML/CFT compliance beyond what direct transaction data reveals.
What do regulators look for in a risk monitoring framework?
Regulators require business-wide documented assessments reviewed annually and aligned to standards like FATF and VARA, with evidence that the framework is actively operated, not just written down.
What’s the main weakness of proof-of-reserves models?
Proof-of-reserves provides a static snapshot that can miss sudden outflows or hidden liabilities, which is why on-chain outflows monitoring and real-time analytics are essential complements rather than optional additions.
